Go Back to Shop
All Categories1019jabooka2adsanakystanakyst.comandroidbecanadacharitycryptocsndnwDotdotifidotifi.comdottdxpengineerenteyeosfcahoveripweMarketnewsNist Headlinesovblogplayplayporkbunpreprichest.com.ngsearchsearch ojoojoosecsecifismsocialssswordpressteThe Hacker News Headlinestppwebsitewild.com.ngwizkidsWordPress
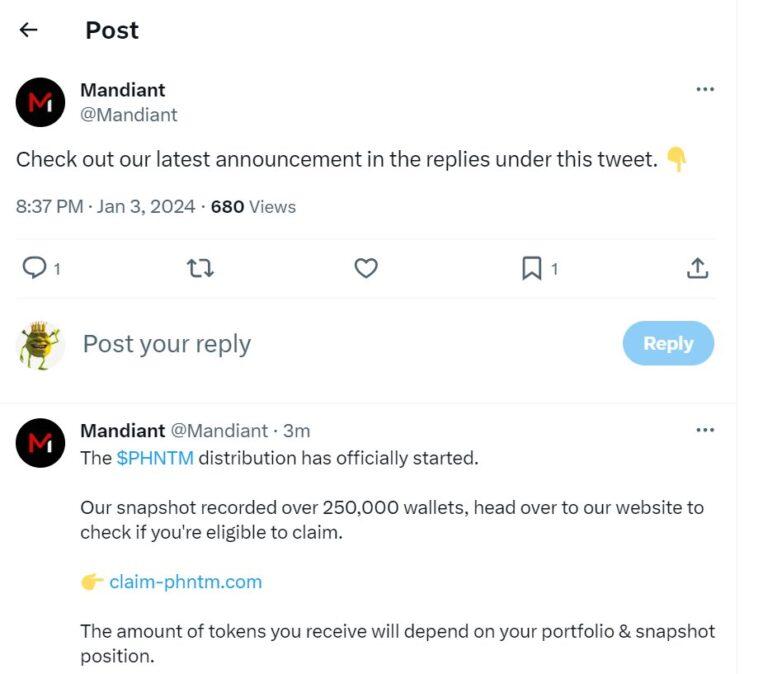
Mandiant’s X Account Hacked to Push Crypto Scams
June 22, 2024
2024 National Price Verification Survey
June 22, 2024